NetScaler Security Design Flaws – Hidden Risks Lurking in Your Architecture
Citrix ADC (formerly NetScaler) sits at the front of many enterprise environments, acting as the entry point for application delivery, remote access, and authentication. Because of this critical role, organisations often assume that once NetScaler Security is deployed, across all their application layers.
In reality, security incidents rarely occur because the technology itself is weak. More often, they arise from architectural design flaws, configuration gaps, or operational oversights around the platform. In many environments, the gateway itself may be well configured. SSL is enabled, multi-factor authentication is in place, and access policies appear correct. Yet other parts of the surrounding infrastructure may remain exposed.
The issue is rarely the gateway. It is the architecture around it.
Attackers rarely target the strongest defence. Instead, they look for the weakest link in the design, the components that was overlooked or assumed to be secure. Here we explore some of the common security design flaws seen in NetScaler environments and why identifying them early is essential for both security resilience and regulatory compliance.
Common NetScaler Security Design Flaws in Environments
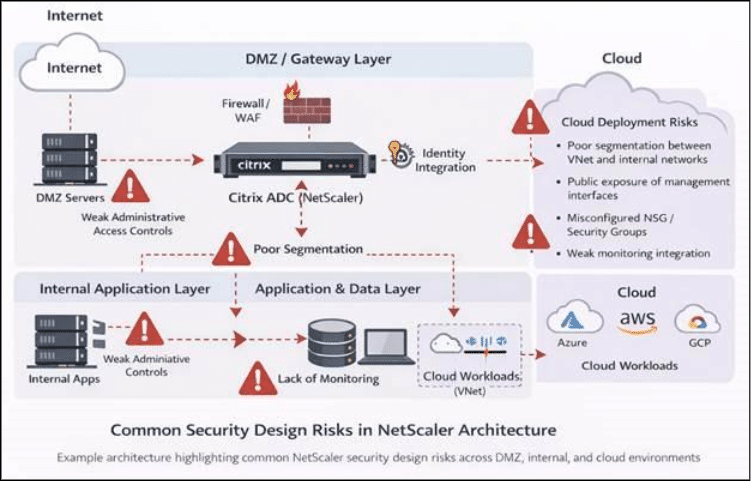
During architecture reviews and security assessments, several recurring issues appear across NetScaler environments. The diagram below highlights some of the key architectural considerations when placing NetScaler within an enterprise environment.
1. Default Credentials and Weak Administrative Controls
One of the most basic but frequently overlooked flaws is leaving default credentials unchanged or granting excessive administrative privileges. This can allow attackers to gain administrative access to the appliance if credentials are exposed or guessed.
Beyond the immediate security risk, weak access control can also create compliance challenges, particularly for organisations subject to regulations such as the General Data Protection Regulation, where accountability and controlled administrative access are expected.
2. Poor Network Segmentation
In some deployments, once traffic passes through the gateway it can communicate freely with multiple internal systems. This creates an opportunity for lateral movement if an attacker gains access to the network.
Segmentation between DMZ infrastructure, application tiers, and backend systems is a common requirement not only for security but also for industry frameworks such as the SWIFT Customer Security Programme used in financial environments.
3. Unsecured Communication Between NetScaler Appliances
High availability configurations improve resilience but can also introduce risk if communication between peer appliances is not properly secured. Weak internal credentials or unsecured management communication can introduce additional attack surfaces within the infrastructure.
4. Excessive Administrative Access Paths
Administrative services such as SSH are often enabled without sufficient restrictions. Features such as SSH tunnelling or port forwarding may unintentionally allow traffic to bypass network controls or reach internal systems.
Restricting administrative pathways is an important principle in infrastructure security and aligns with guidance in regulations such as the NIS Directive, which focuses on protecting critical infrastructure systems.
5. Outdated Firmware and Unpatched Vulnerabilities
Another common operational flaw is running unsupported or outdated firmware. Like any infrastructure platform, NetScaler software receives regular updates that address security vulnerabilities and performance issues. Failing to maintain current versions increases the likelihood that known vulnerabilities could be exploited.
6. Limited Monitoring and Security Visibility
Many organisations deploy NetScaler but do not implement sufficient monitoring of gateway activity. Without proper logging and analysis, suspicious behaviour or early indicators of compromise can easily go unnoticed. Security frameworks increasingly require organisations to demonstrate monitoring, audit trails, and incident detection capabilities across critical systems.
7. Cloud Deployment Design Considerations
As organisations increasingly deploy NetScaler instances in public cloud environments such as Microsoft Azure, Amazon Web Services, and Google Cloud, additional architectural considerations come into play. In cloud deployments, security responsibilities are shared between the cloud provider and the customer. Misconfigured network security groups, overly permissive routing rules, or direct exposure of management interfaces can introduce significant risks. It is important to ensure that NetScaler instances are deployed within properly segmented virtual networks, with restricted administrative access and appropriate monitoring controls in place. Cloud environments also introduce new operational considerations such as secure integration with identity services, logging, and compliance with organisational security policies.
Security Design Is More Than Configuration
These issues rarely occur because administrators lack technical knowledge. In most cases, they arise because security and compliance requirements were not considered early enough during the design phase.
Infrastructure security is not just about deploying appliances — it is about how those components integrate within the broader architecture.
Why Architecture and Compliance Must Be Considered Together
Organisations operating in regulated industries must also ensure that infrastructure design aligns with relevant standards and regulatory frameworks. These frameworks typically require strong access controls, network segmentation, monitoring, and incident response capabilities:
- General Data Protection Regulation (GDPR)
- NIS Directive
- SWIFT security controls for financial systems
Poor architectural decisions can lead not only to security vulnerabilities but also to audit failures or regulatory exposure.
Time to look beyond the Gateway
NetScaler remains a highly capable and secure application delivery platform when deployed correctly. However, its effectiveness depends heavily on how the surrounding architecture is designed and managed. Security gaps rarely arise from the technology itself, but from design decisions that overlook network segmentation, access control, monitoring, or compliance considerations. Treating NetScaler as part of a broader security architecture, alongside identity platforms, network controls, and monitoring systems, helps organisations reduce risk and strengthen their overall security posture.
As a Citrix Platinum Partner, Enterprise Solutions works closely with organisations to assess NetScaler environments, identify potential security design gaps and support secure, compliant architectures. Our Citrix specialists provide architecture reviews, security assessments, upgrades and ongoing operational support to ensure NetScaler deployments remain resilient and aligned with industry best practices. To learn more or discuss your environment with our team, contact us at asktheexpert@enterprise-solutions.ie
At Enterprise Solutions, our work starts with listening. As a Citrix Platinum Partner and Citrix Preferred Services Provider, our Citrix specialists bring deep, hands‑on experience from supporting real‑world NetScaler environments across a wide range of industries. We take the time to understand how your platform is designed, how it is used day to day, and where architectural risks may quietly emerge over time.
Drawing on this experience, we help organisations identify security design gaps, make informed architectural decisions, and strengthen NetScaler environments in a way that supports both operational needs and regulatory requirements. From architecture reviews and security assessments to upgrades and ongoing support, our team works alongside yours to ensure NetScaler remains resilient, well‑governed, and aligned with industry best practice.
If you would like an expert perspective on your environment, Simply contact us at asktheexpert@enterprise-solutions.ie.

Narendra is a seasoned expert with over 18 years of experience in Mobility, Network Security, and Cloud. He has successfully designed and integrated End-User Computing (EUC) solutions across industries such as FSI, Banking, Manufacturing, Shipping, and Consulting. With a strong customer-first approach, he ensures seamless implementation, driving customer success and delivering tangible business value.




