deviceTRUST – taking your zero-trust strategy to the next level
User credentials get compromised. This is a fact of life. Organizations use multi-factor authentication mechanisms to try to reduce the attack surface, but even these are not always 100% effective and breaches will happen. So, we have user authentication as a factor, and we have other solutions to provide a second factor. Imagine if we could make the device an additional factor, and make that contextual aware also? This is where deviceTRUST, a recent Citrix acquisition, comes to the fore. If you have renewed to the Citrix Universal Hybrid Multi Cloud (UHMC) license, you are now entitled to this.
With deviceTRUST, organizations can monitor a vast array of different properties and configurations from the endpoint accessing the Citrix session, and have contextual awareness of these, reacting in real-time to changes and acting.
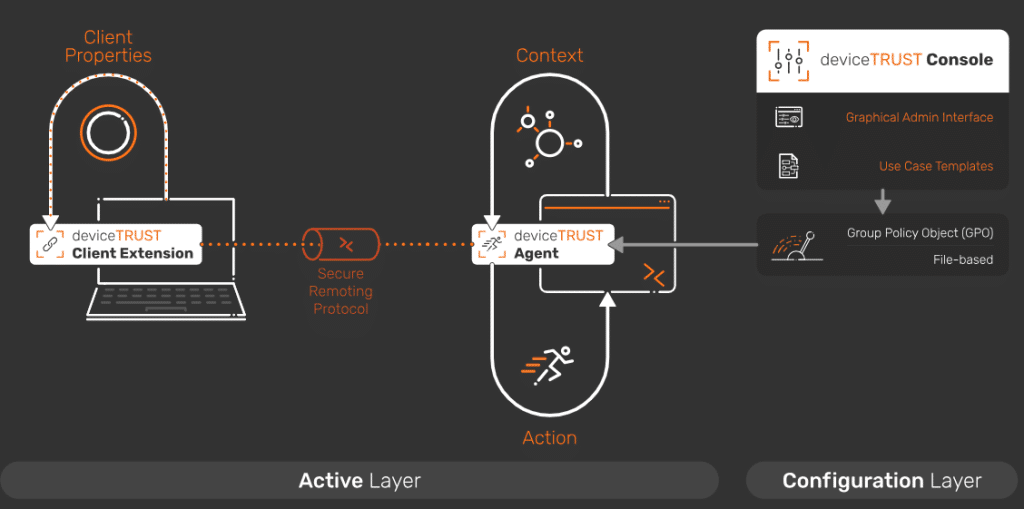
The deviceTRUST architecture is simple to implement. There are 3 main components to consider. From the endpoint that is connecting, there is the deviceTRUST client extension. This communicates securely through a virtual channel in the ICA session to the deviceTRUST agent is that installed on the Citrix VDA. The deviceTRUST agent is receiving its configuration from the deviceTRUST console. This can be done via Group Policy or via a file-based method. There is no additional infrastructure required.


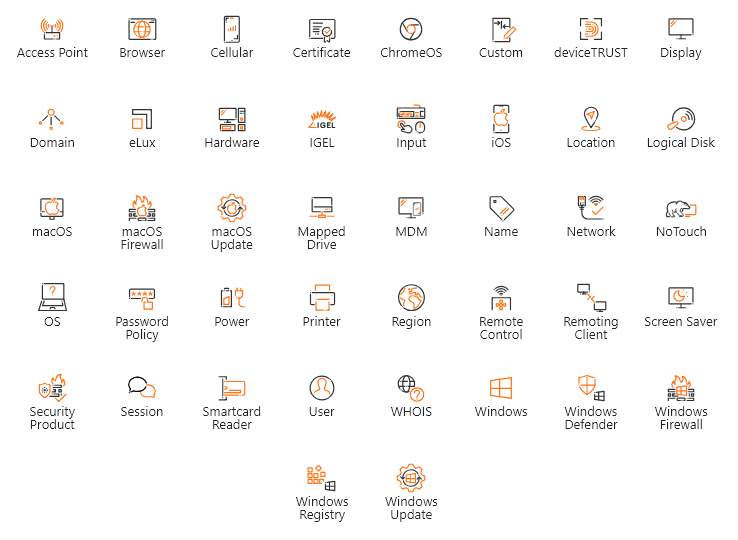
When we look at the different categories that are available for deviceTRUST to monitor on the endpoint, it is extensive. It can look at everything from browsers, hardware, network, and OS components.
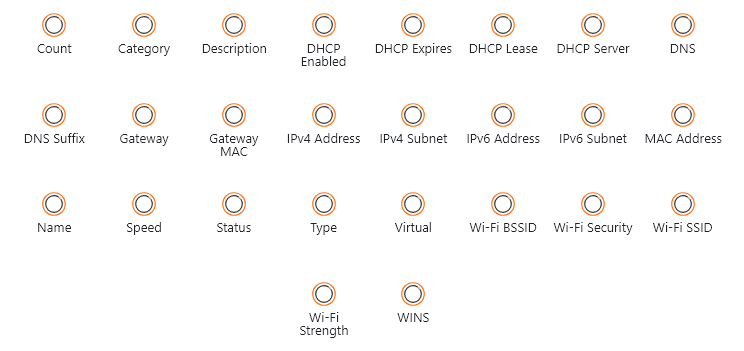
If I dive deeper into one of these, Network for example, you will see the wide array of properties that can be configured.
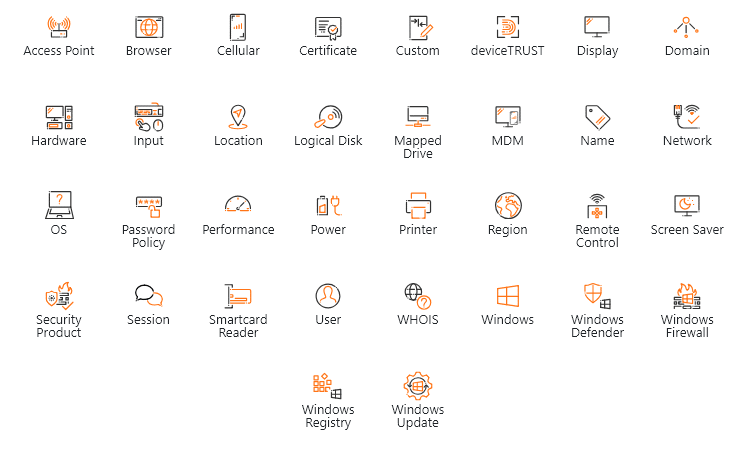
You can also configure deviceTRUST to monitor different categories and properties within the VDA itself by the agent.
Let’s go through a few examples of how you can use deviceTrust to take your zero-trust posture to the next level.
Unauthorized USB Devices
In this example, I have configured a policy to only allow my iPhone 13 to be connected to my endpoint while using my Citrix session. This is done by using the Vendor and Product Id’s. For any other USB device that is connected, it will deny access to the session.
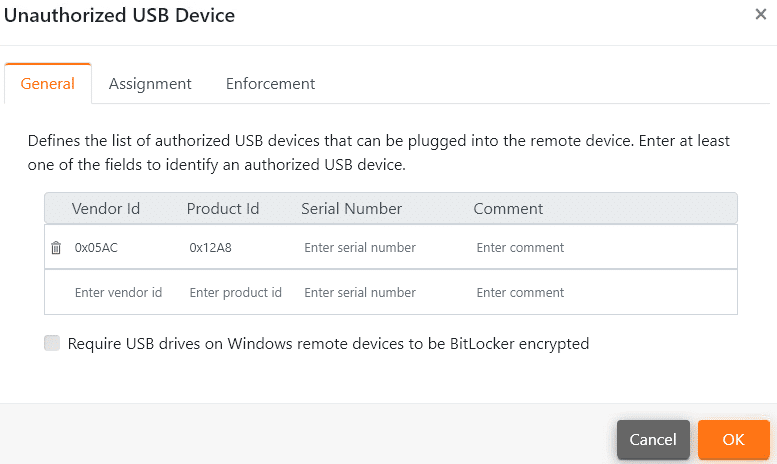
When I plug in a USB thumb drive, the deviceTRUST client extension on my endpoint detects this and sends the context change to the agent on the VDA. The agents reacts and in real-time denies access to the Citrix session. Once the unauthorized USB device is removed, the session resumes.
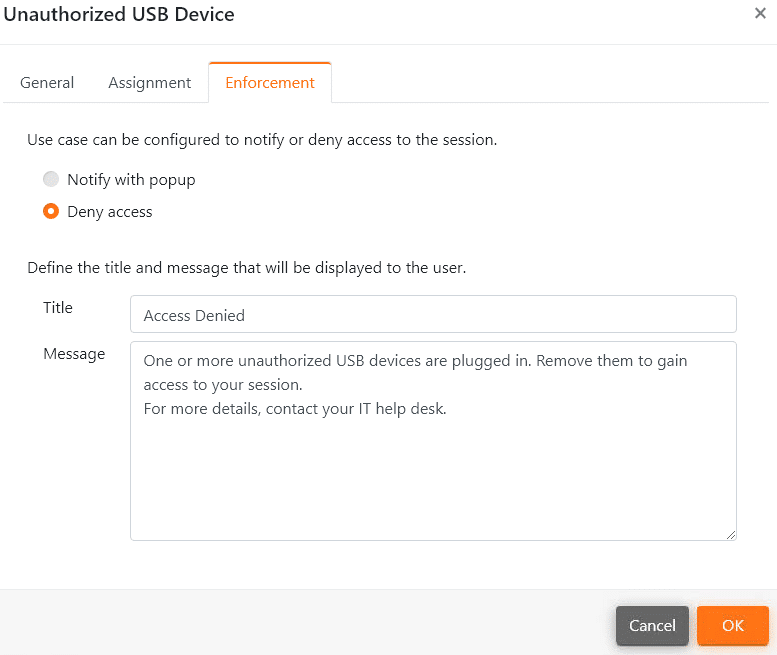
Registry Change
In this example, deviceTRUST is configured to monitor a specific registry key that enables or disables a security product. If the key is set to TRUE, no action is required. However, if the key is set to FALSE, it will detect this and deny access to the session.
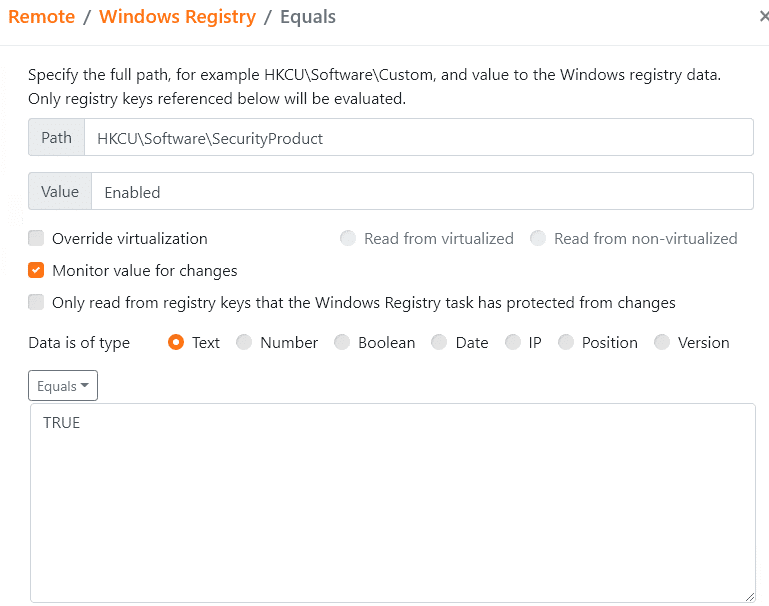
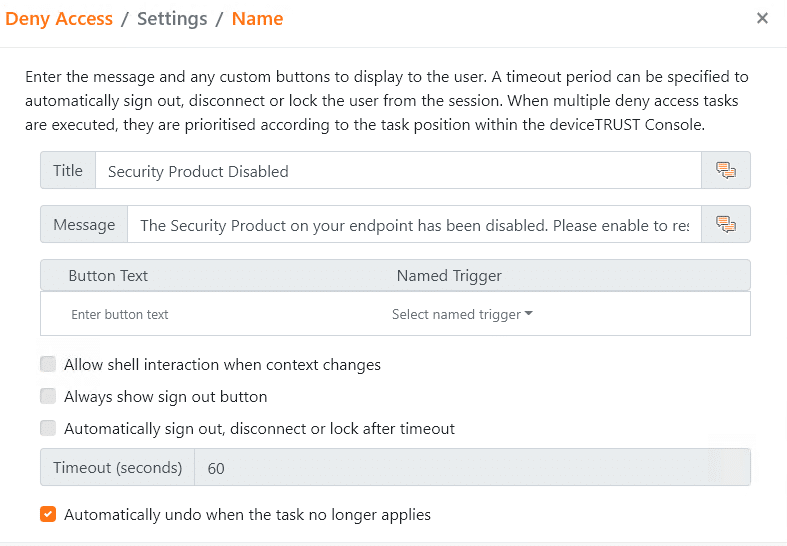
Again, the real power of deviceTRUST is shown here in how it reacts in real-time to the registry changes on the endpoint.
Network Type Change
In the final example, I am simulating having a high confidential financial application running in the Citrix session and I want to ensure that is only available on certain types of networks. To achieve this, deviceTRUST is configured to monitor the network type that the user is connected to. If the network type is private, no action is taken. If it is anything other then private, it will terminate and restrict access to the application using AppLocker.
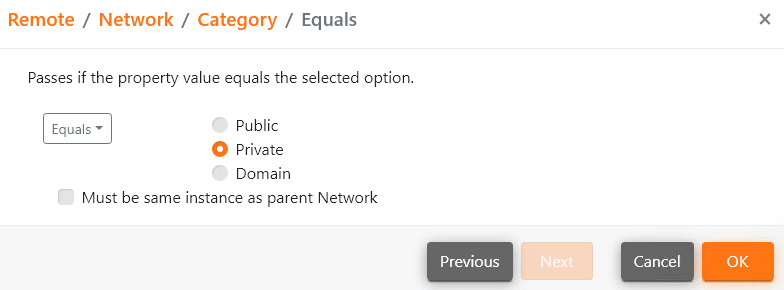
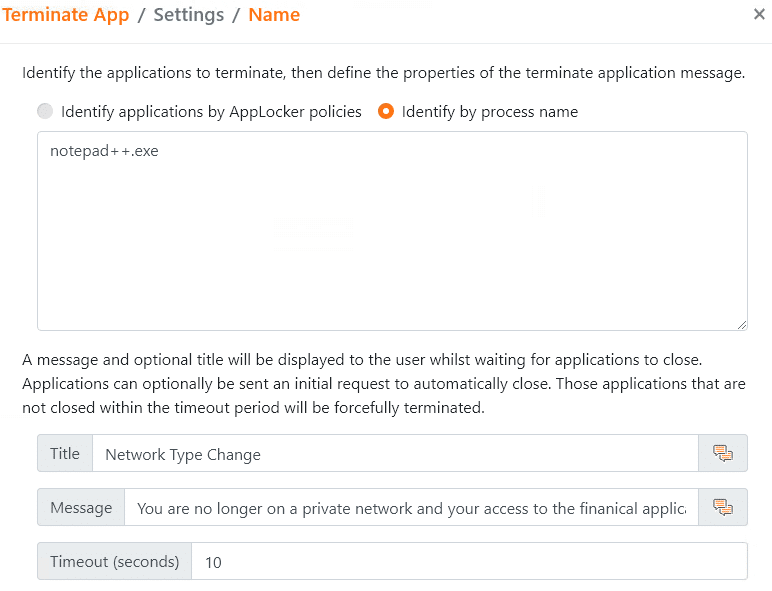
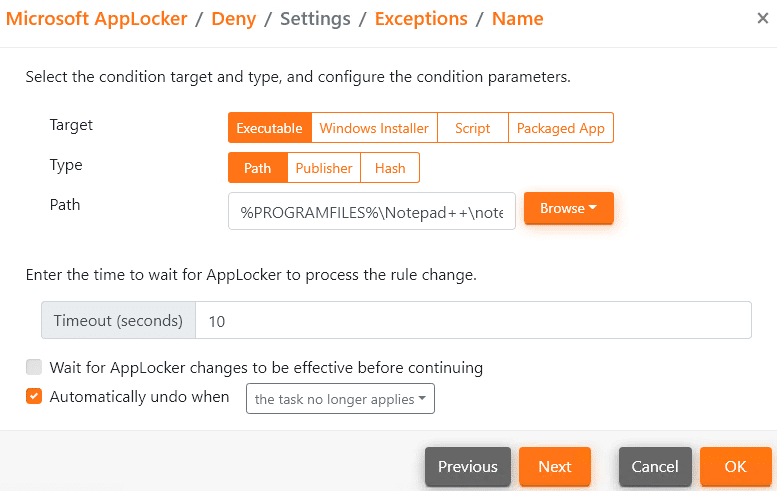
Once the network type is detected as being private again, access to the application is enabled again.

Hopefully this has given you an understanding of the power and granularity that deviceTRUST can bring to your zero-trust strategy. As mentioned, this is included in the Citrix UHMC license so you may be already entitled to start using it today!

Shane O’Neill is a Citrix CTP/ EUC Architect here at Enterprise Solutions. He loves automation. Shane is constantly coding in C# and PowerShell to create new tools to make his life and that of other Citrix admins easier, and to fill in the gaps in automation and reporting that Citrix doesn’t currently provide. Holding certifications in Citrix, VMware, Cato Networks, Microsoft and Hyper-V to name just a few. Shane was named one of the first Citrix Technology Advocates in 2016 and has held the title of Citrix Technology Professional since 2019, one of only 60 worldwide.




