NetScaler Security Design Flaws (Pt2): When Credentials Become the Attack Vector
In my previous article on NetScaler security design flaws, I explored architectural risks across gateway and infrastructure layers. In this article, I want to focus on how credential-based attacks are evolving and why identity design is now a critical part of NetScaler security.
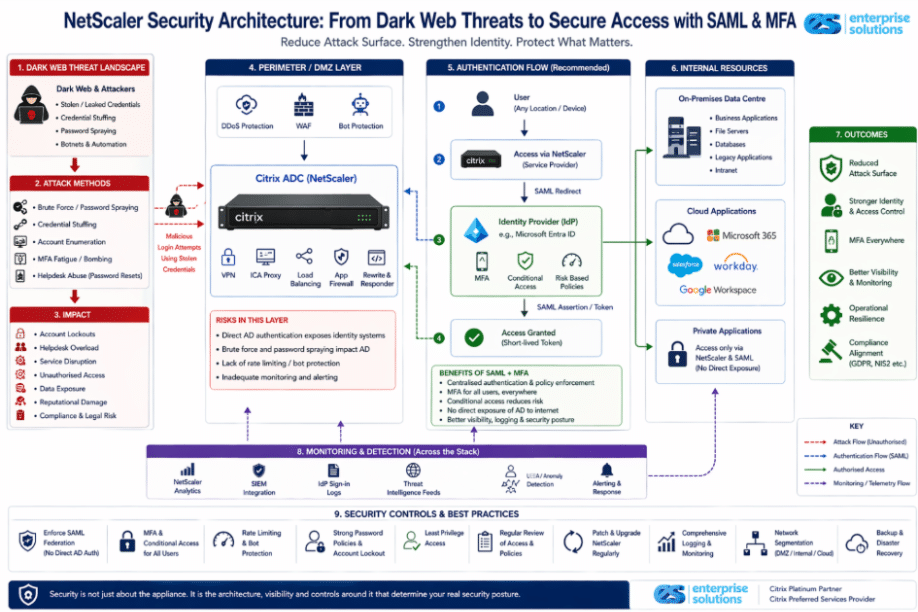
As identity‑centric attacks continue to rise, platforms like Citrix NetScaler are increasingly evaluated not just on traditional perimeter security, but on how effectively they integrate with modern identity and access management frameworks. Search trends show growing focus on topics such as credential‑based attacks, password spraying, identity federation, and SAML authentication. In this context, NetScaler security is no longer just about appliance hardening, it is about designing resilient authentication flows that minimise risk, reduce exposure of Active Directory, and adapt to evolving threat behaviour.
As you are probably aware, NetScaler sits at the front of many enterprise environments, acting as the entry point for application delivery, remote access, and authentication. Because of this critical role, organisations often assume that once NetScaler is deployed, their access layer is secure.
In reality, modern attacks are shifting that assumption. Security incidents today are less about weaknesses in the appliance itself and more about how identity, authentication, and architecture are designed around it.
How Dark Web Credentials Are Used in Modern Access Attacks
Dark web credentials are no longer just a passive data exposure risk, they are now being actively used as part of targeted attack strategies.
Attackers are not simply logging in with stolen passwords. Instead, they are:
- using large credential datasets to generate authentication attempts,
- triggering password resets and account lockouts,
- overwhelming helpdesks and operational teams,
- probing identity systems to identify valid users and policies,
- exploiting authentication workflows across gateways,
In this model, credentials are not just used for access, they are used to test and weaken the entire authentication layer.
Where NetScaler Becomes a Target
In many environments, NetScaler acts as the front-line authentication gateway, handling VPN access, ICA proxy sessions, and integration with identity services. As a result, it becomes one of the first places where credential-based attacks surface.
Typical indicators include:
- spikes in failed login attempts,
- abnormal authentication patterns across multiple users,
- increased load on MFA and identity systems,
- repeated session failures or lockouts,
If the underlying design relies heavily on direct Active Directory authentication, these attacks can place significant pressure on core identity infrastructure.
The Hidden Risk of Direct Active Directory Authentication
A common architectural pattern is to authenticate users directly against Active Directory (via LDAP or RADIUS) at the gateway. While this works functionally, it introduces risk:
- repeated login attempts directly impact AD
- password spraying and credential stuffing can trigger lockouts
- attackers can indirectly enumerate users and policies
- helpdesk load increases due to account resets and failures
This model exposes internal identity systems more directly than necessary.
Strengthening NetScaler Security with SAML and Identity Federation
A more secure and modern approach is to federate authentication using SAML, integrating NetScaler with an identity provider such as Microsoft Entra ID.
In this model:
- NetScaler acts as a service provider,
- authentication is redirected to the identity provider,
- MFA and conditional access policies are enforced centrally,
- authentication decisions are made outside the gateway,
This shifts the control point from the gateway to a centralised identity platform, allowing for:
- consistent MFA enforcement,
- adaptive access based on risk, device, and location,
- reduced exposure of traditional AD authentication paths,
- improved visibility into authentication behaviour,
What the Architecture Reveals
The architecture diagram in this article highlights how these elements interact.
It demonstrates:
- how authentication flows from the internet through the NetScaler gateway,
- where weak administrative controls and poor segmentation introduce risk,
- how attackers use credential-based techniques to probe authentication systems,
- how cloud environments can extend the attack surface if not properly secured,
It also reinforces a key point:
Security risks often emerge not from a single component, but from how multiple layers interact under real-world conditions.
Operational, Security, and Compliance Impacts of Poor Identity Design
These attacks do not just affect security, they impact operations, users, and business continuity. Organisations may experience:
- helpdesk overload due to password resets and lockouts,
- degraded performance across authentication systems,
- increased risk of unauthorised access,
- exposure of sensitive internal applications,
- downstream impact on customers and partners,
From a regulatory standpoint, frameworks such as General Data Protection Regulation and NIS2 Directive expect organisations to demonstrate strong controls around identity, access, monitoring, and incident response. Architectural weaknesses in authentication design can lead to both security incidents and compliance challenges.
Why NetScaler Security Must Be Designed, Not Assumed
These evolving attack patterns highlight a fundamental principle: security is not just about securing the gateway; it is about securing the entire authentication and access flow.
Even with a well-configured NetScaler deployment, risks can emerge if:
- authentication relies heavily on direct AD interaction,
- identity policies are inconsistent,
- monitoring and logging are limited,
- cloud integrations are not properly controlled,
A resilient design requires:
- strong identity federation (SAML),
- enforced MFA and conditional access,
- controlled exposure of internal systems,
- continuous monitoring of authentication behaviour,
Designing a Resilient NetScaler Authentication Architecture
NetScaler remains a highly capable and secure application delivery platform when deployed correctly. However, its effectiveness depends heavily on how the surrounding architecture is designed and managed. Security gaps rarely arise from the technology itself, but from design decisions that overlook network segmentation, access control, monitoring, or compliance considerations. Treating NetScaler as part of a broader security architecture, alongside identity platforms, network controls, and monitoring systems, helps organisations reduce risk and strengthen their overall security posture.
At Enterprise Solutions, our work starts with listening. As a Citrix Platinum Partner and Citrix Preferred Services Provider, our specialists bring deep, hands‑on experience supporting NetScaler environments across a wide range of industries. By taking the time to understand how your platform is designed, how it is used day to day, and where architectural risks may quietly emerge, we help organisations identify security design gaps, make informed architectural decisions, and strengthen NetScaler environments in a way that supports both operational needs and regulatory requirements. From architecture reviews and security assessments to upgrades and ongoing support, our team works alongside yours to ensure NetScaler remains resilient, well‑governed, and aligned with industry best practice.
If you would like an expert perspective on your environment, simply contact us at asktheexpert@enterprise-solutions.ie

Narendra is a seasoned expert with over 18 years of experience in Mobility, Network Security, and Cloud. He has successfully designed and integrated End-User Computing (EUC) solutions across industries such as FSI, Banking, Manufacturing, Shipping, and Consulting. With a strong customer-first approach, he ensures seamless implementation, driving customer success and delivering tangible business value.




